An Introduction to TrustZone
2017 年 09 月 15 日 ソリューション統括部
The Internet of Things (IoT) is growing at an excellent pace, with connected embedded intelligence becoming an integral part of people's lives at an individual, industrial and societal level. ARM TrustZone technology is a system-wide approach to security for system-on-chip (SoC) designs. It is hardware-based security built into the heart of CPUs and systems and used by semiconductor chip designers who want to provide security to devices, such as root of trust. TrustZone technology is available on any ARM Cortex-A based system.
So what is Trust Zone?
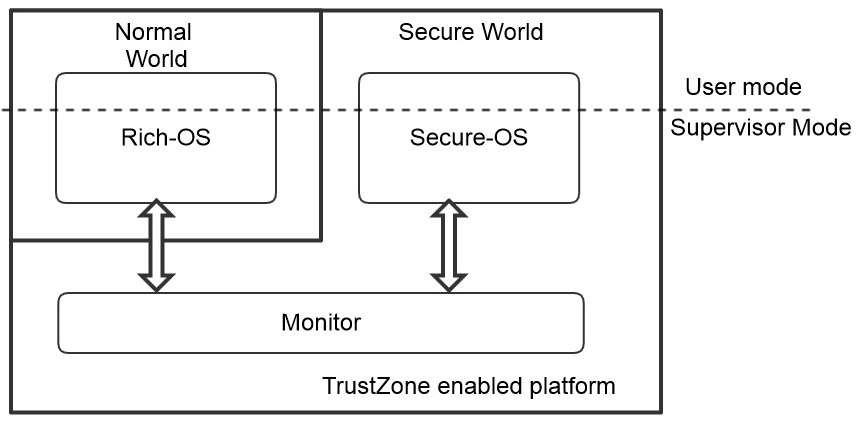
At the heart of the TrustZone approach is the concept of secure and non-secure worlds that are hardware-separated from each other. Within the processor, software either resides in the secure world or the non-secure world; a switch between these two worlds is accomplished via software in Cortex-A processors (referred to as the secure monitor). This concept of secure (trusted) and non-secure (non-trusted) worlds extends beyond the CPU. It also covers memories, on-chip bus systems, interrupts, peripheral interfaces and software within a SoC.
There is a Four Compartment Security model implemented in ARM. They are as below:
- Normal World - With which USER/SYSTEM modes will work
- Hypervisor Mode - were Virtual OS can run
- Trusted World - were trusted application and OS resides.
- Secure Elements - offering Tamper proof secured processing and storage.
The Following is the Outline of Trusted Zone
Features of ARM TrustZone
The main Features of ARM TrustZone are as follows:
- TrustZone provides Hardware Isolation
Each of the Physical cores will be divided into two virtual isolated cores with names Secure World and Normal World. - Monitor Mode
This is a mechanism to switch between secure mode and normal mode. In other words we could say this monitor mode as the gate keeper to secure world. Monitor Mode can be selected by using SMC (Secure Monitor Calls) instructions and by some exceptions. - CPU state is carried out to the AXI bus
Secure mode can be enabled by setting AXI bus bit AxProt [1]. A '0' here means secure and a '1' means non secure mode. This will allow implementation of secure-aware peripherals.
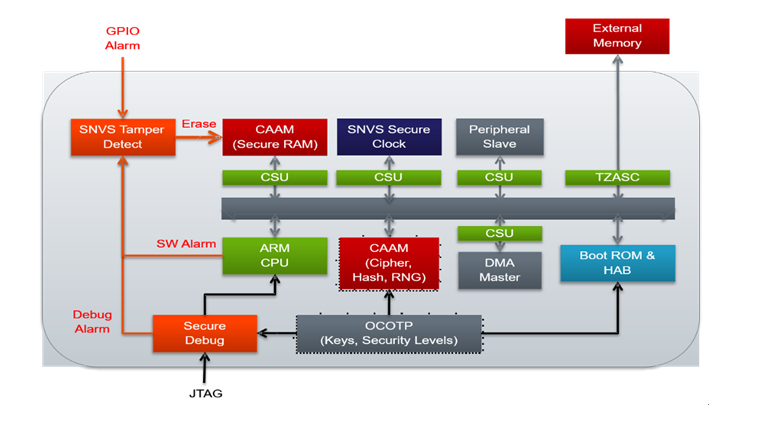
As an Example Let us look into the Trust Zone Architecture of NXP's i.MX SoC.
How Arm TrustZone Works
From the block diagram above we could distinguish what are the special internals that constitute the TrustZone environment in i.MX. The main components that constitute TrustZone in i.MX are as follows:
- Generic Interrupt controller (GIC):- Used to distinguish the interrupts from secure world and non-secure world
- TrustZone Watchdog Timer (TZ WDOG): - The TrustZone Watchdog (TZ WDOG) timer module protects against TrustZone starvation by providing a method of escaping normal mode and forcing a switch to the TZ mode. TZ starvation is a situation where the normal OS prevents switching to the TZ mode. Such a situation is undesirable as it can compromise the system's security.
- TZ Address Space Controller (TZASC):- The TZASC provides security address region control functions required for intended application. It is used on the path to the DRAM controller.
- Central Security Unit (CSU):- will determine the security level operation mode as well as the TZ policy. CSU enforces the access rights to peripherals for secure and non-secure modes
Working of TrustZone in Freescale i.MX SoC's.
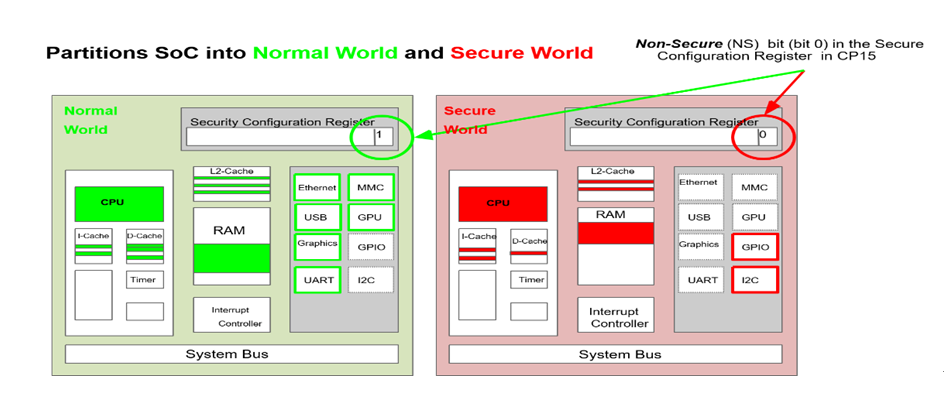
TrustZone functionality depends on the SCU register. As you can see in the following figure the NS bit in Secure Configuration Register decides the TrustZone Functionality of the SoC.
By setting '0' to the NS bit in SCU makes the TrustZone configured memory and Peripherals to go live.
How to Secure Peripherals?
This can be done by the CSU. Each peripherals including DMA peripherals can be configured separately for TrustZone. These peripherals will be monitored by CSU.
How to Secure Memory?
TZASC (TrustZone Address space controller) will do the secure memory Management for TrustZone. There will be separate MMU Page tables, TLB and Cache memory for secure and non-Secure operations. TZASC will isolate secure memory and non-secure memory from each other. Each of the eight memory (in the case of i.MX) regions can be configured with different security permissions.
CPU Architecture support for ARM TRustZone
For supporting TrustZone, ARM has implemented an Extra processor execution level called EL3 in ARMv8 and Secure Monitor in ARMv7. Secure Monitor Calls are used to get the CPU enter into EL3 Mode.
Memory Architecture support for ARM TRustZone
MMU provides 2 virtual address spaces separately for Secure and non-secure world operations. The TLB and cache entries will have an additional tag to identify the world (Secure or Non-Secure world) that used it.
Posted by vi
記事カテゴリ別新着一覧
Vigiles サポート
Vigiles ファーストステップガイド 4 「SBOM ダッシュボードの使い方」
2025 年 05 月 14 日 Vigiles サポート
Vigiles ファーストステップガイド 3 「Build root 環境の Vigiles 導入手順」
2024 年 09 月 02 日 Vigiles サポート
Vigiles ファーストステップガイド 2 「Yocto 環境への Vigiles 導入手順」
2024 年 03 月 01 日 Vigiles サポート
Yocto Project よもやま話
Yocto よもやま話 第 19 回 「Yocto Project 5.3 Whinlatter」
2026 年 02 月 09 日 Yocto Project よもやま話
Yocto よもやま話 第 18 回 「Yocto Project 5.2 Walnascar」
2026 年 02 月 09 日 Yocto Project よもやま話
Yocto よもやま話 第 17 回 「Yocto Project 5.1 Styhead」
2026 年 02 月 09 日 Yocto Project よもやま話
Linux 技術ネタ
RISC-Vについて学ぶ-後編
2024 年 01 月 10 日 Linux 技術ネタ
RISC-Vについて学ぶ-前編
2023 年 12 月 12 日 Linux 技術ネタ
デバイスツリーとサウンド設定(widgets, routing)について学ぶ:後編
2023 年 03 月 31 日 Linux 技術ネタ
イベントレポート
EdgeTech+ 2025 出展レポート
2025 年 12 月 01 日 イベントレポート
EdgeTech+ West 2025 出展レポート
2025 年 08 月 08 日 イベントレポート
EdgeTech+ 2024 出展レポート
2024 年 12 月 06 日 イベントレポート
リクルート
新卒採用、絶賛募集中!
2025 年 04 月 01 日 リクルート
新卒採用、絶賛募集中!
2023 年 05 月 30 日 リクルート
大しごとーく & オープン・カンパニー in 信州 2022
2022 年 12 月 27 日 リクルート
信州リネオ便り
旧制松本高等学校を歩く
2026 年 04 月 09 日 信州リネオ便り
奈良井宿アイスキャンドル祭りに行ってきました
2026 年 02 月 09 日 信州リネオ便り
2026年 明けましておめでとうございます
2026 年 01 月 06 日 信州リネオ便り
ソリューション統括部
Zephyrブログ 第一回 はじめての Zephyr(前編)
2026 年 03 月 18 日 ソリューション統括部
シリコンバレー探検記 2019 ~番外編~
2019 年 12 月 10 日 ソリューション統括部
シリコンバレー探検記 2019 ~後編~
2019 年 12 月 10 日 ソリューション統括部
マーケティング統括部
大成功決起大会!!(ET2019)
2019 年 12 月 13 日 マーケティング統括部
ESEC 2019 決起大会
2019 年 04 月 25 日 マーケティング統括部
シリコンバレー探検記 その 2
2018 年 12 月 18 日 マーケティング統括部






















